Considerations for building HIPAA compliant websites and applications
Figure 1.1. Asymmetric risk profile graphic (see article for more information)
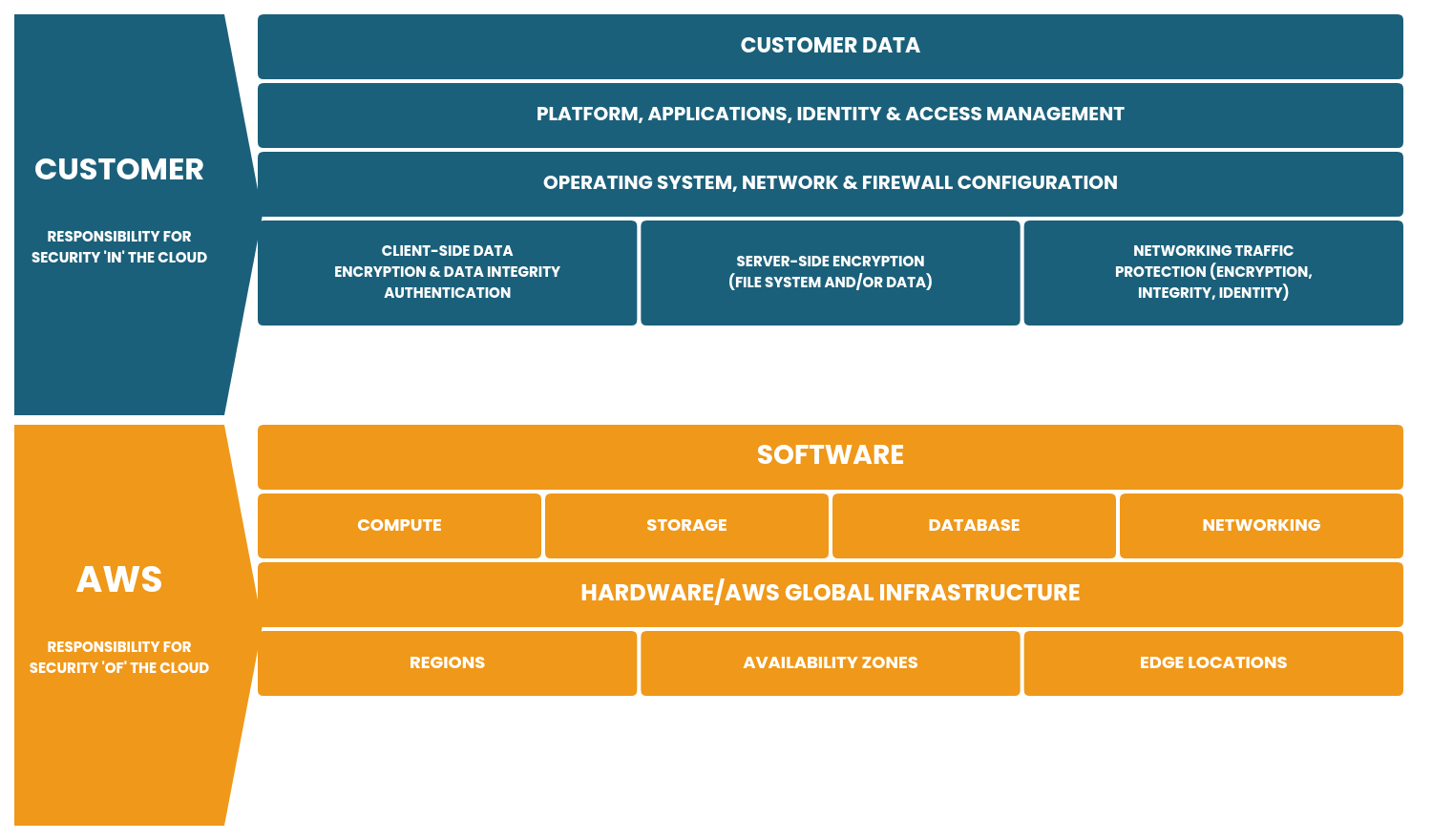
Figure 1.2. Dev ops shared security model
Source: https://aws.amazon.com/compliance/shared-responsibility-model